Ways To Wiretap Child’s Mobile Phone

Choosing the right parental monitoring app protects your child online while respecting their growing need for privacy.
Hoverwatch leads as the top parental monitoring app for Android. See our full review.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
This information is for educational purposes only. Unauthorized access to someone else’s device or accounts is illegal. Use these methods only on devices you own or with proper legal authorization.
What About Understanding the Parental Monitoring Dilemma?
Modern parents face unprecedented challenges.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
Children receive smartphones at age 10-11 on average, with access to unlimited content and potential dangers.
Legitimate Parental Concerns
Parents have valid reasons to monitor children’s device usage:
- Cyberbullying: Online harassment can have devastating psychological effects on children
- Predatory behavior: Adults may attempt to groom or exploit children through messaging apps and social media
- Inappropriate content: Easy access to violent, sexual, or disturbing material
- Social media risks: Oversharing personal information, inappropriate posts affecting future opportunities
- Screen time management: Excessive device use affecting sleep, academic performance, and physical health
- Location safety: Knowing where children are for emergency situations
- Digital citizenship: Ensuring children behave appropriately online
- Academic integrity: Monitoring that devices are used appropriately for schoolwork
However, monitoring also raises concerns about trust, privacy, autonomy, and the parent-child relationship. Finding the right balance requires understanding both the available tools and the broader implications of surveillance.
“The most effective security measures are often the simplest: strong unique passwords, two-factor authentication, and keeping your software updated. Most breaches exploit basic oversights, not sophisticated vulnerabilities.”
Alex Rivera, CEH, OSCP
What About Legal Framework for Parental Monitoring?

Before implementing any monitoring solution, understand the legal landscape.
Legal Parental Rights
In most jurisdictions, parents have broad legal authority to monitor minor children’s devices:
- Parents can legally monitor children under 18 in most regions
- No consent from the child is legally required
- Parents can install monitoring software on devices they own or provide
- Access to children’s accounts and communications is generally permitted
- School-issued devices may have separate policies and restrictions
Apply these security measures consistently to protect your devices and accounts from unauthorized access.
Legal Limitations
Some restrictions do apply:
- Monitoring becomes illegal once children reach age of majority (18 in most places, varies by jurisdiction)
- Using monitoring data to blackmail, harass, or harm the child may be illegal
- Sharing private information about children online without consent may violate privacy laws
- Recording conversations involving other children or adults may have legal implications
- Some jurisdictions require two-party consent for call recording
- School policies may restrict certain monitoring during school hours
Never install monitoring software on devices you do not own — unauthorized installation violates federal wiretapping laws.
Important Considerations
Legal doesn’t always mean advisable:
- Courts may consider monitoring practices in custody disputes
- Excessive or inappropriate monitoring can be cited as evidence of poor parenting
- Teens approaching adulthood deserve increasing privacy
- Invasive monitoring can damage parent-child relationships
- Transparency generally produces better outcomes than covert surveillance
What About Approaches to Parental Monitoring?

1. Transparent Monitoring with Communication
Research consistently shows that open communication about monitoring produces better outcomes than secret surveillance.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
Best practices:
- Discuss internet safety before giving children devices
- Explain why monitoring exists and what you’ll be checking
- Set clear expectations about appropriate device use
- Review monitoring results together when concerns arise
- Gradually reduce monitoring as children demonstrate responsibility
- Focus on safety rather than control
- Respect age-appropriate privacy needs
Security researchers consistently find that basic protective measures prevent over 80% of common surveillance attempts.
Age-appropriate transparency:
- Ages 6-10: Full monitoring with regular discussions about what you see
- Ages 11-13: Monitoring with periodic check-ins and conversations about digital citizenship
- Ages 14-16: Reduced monitoring with emphasis on trust and responsibility
- Ages 17-18: Minimal monitoring, respecting increasing autonomy while maintaining safety checks
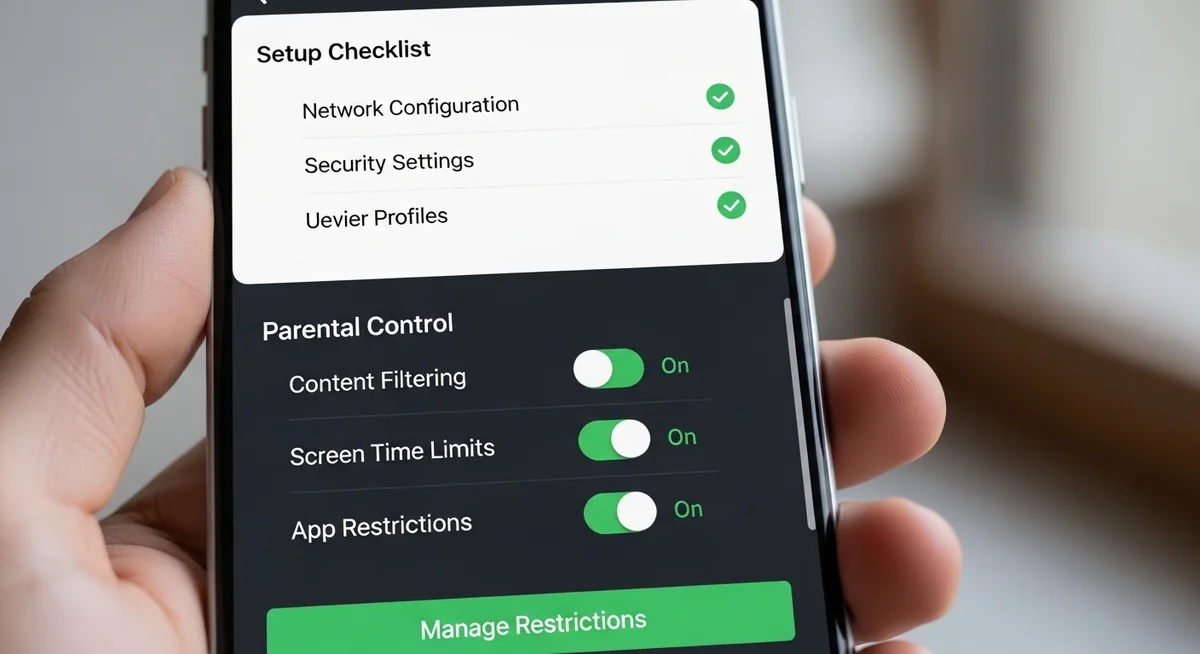
2. Built-in Operating System Parental Controls
Both iOS and Android offer robust parental control features that should be your first choice. These are free, integrated into the operating system, and designed specifically for family use.
iOS – Screen Time Features:
Apple’s Screen Time provides comprehensive parental controls:
- Downtime: Schedule times when only essential apps and calls are available
- App limits: Set time limits for specific app categories or individual apps
- Communication limits: Control who children can communicate with during screen time and downtime
- Content & privacy restrictions: Block inappropriate content, prevent purchases, restrict explicit content
- Always allowed apps: Specify apps that work even during downtime (phone, messages, educational apps)
- Location sharing: See child’s location through Find My
- Screen time reports: Detailed breakdowns of how child uses device
- App installation controls: Require approval before installing apps
Setting up Screen Time:
- Settings → Screen Time → Turn On Screen Time
- Select “This is My Child’s iPhone”
- Set up Downtime schedule
- Configure App Limits
- Set Communication Limits
- Enable Content & Privacy Restrictions
- Create a Screen Time passcode (different from device passcode)
Android – Family Link Features:
Google’s Family Link provides similar comprehensive controls:
- App management: Approve or block app installations from Google Play
- Screen time limits: Set daily limits and bedtime schedules
- App activity reports: See which apps children use and for how long
- Location tracking: See child’s location when device is powered on
- Remote device locking: Lock device remotely when it’s time for bed or homework
- Content filtering: Filter inappropriate websites in Chrome
- Purchase approvals: Approve or decline purchase requests
- Safe Search: Enable filtered search results on Google
Setting up Family Link:
- Download Family Link app on parent’s device
- Follow setup process to create child account or supervise existing account
- Install Family Link on child’s device
- Configure controls through parent app
- Child cannot uninstall Family Link without parent approval
3. Monitoring Applications for Enhanced Oversight
When built-in features are insufficient, third-party monitoring apps provide more comprehensive tracking. These should be used transparently with children’s knowledge.
mSpy:
One of the most popular parental monitoring solutions:
- Location tracking: Real-time GPS location with location history
- Call monitoring: View call logs, record calls (where legally permitted)
- Message monitoring: SMS, MMS, and messaging app content
- Social media tracking: WhatsApp, Instagram, Snapchat, TikTok, Facebook, Telegram, Discord
- Internet activity: Browsing history, bookmarks, searches
- Geofencing: Alerts when child enters or leaves designated areas
- Screen time reports: Detailed device usage analytics
- Keylogger: Record keystrokes (controversial feature)
- Remote control: Block apps or websites remotely
Pricing: Subscription-based, typically $30-70/month depending on features and number of devices
Compatibility: iOS 10+ and Android 4.4+, though iOS features are limited without jailbreaking
HighsterMobile:
Focused on social media monitoring:
- Social media emphasis: Comprehensive tracking of Instagram, TikTok, Snapchat, Discord
- Message access: Read all incoming and outgoing messages
- Multimedia access: View photos and videos shared or received
- Contact access: See all contacts and communication patterns
- Location tracking: GPS location with history
- Remote messaging: Send messages from monitored device remotely
- Data deletion: Remotely delete inappropriate content
Apply these security measures consistently to protect your devices and accounts from unauthorized access.
Installation: Requires brief physical access to child’s device (10-15 minutes)
FlexiSPY:
Advanced monitoring with extensive features:
- Call recording: Record phone calls on both cellular and VoIP apps
- Ambient recording: Activate microphone remotely to hear surroundings
- Camera control: Take photos remotely using phone’s cameras
- Live call listening: Listen to calls in real-time
- Comprehensive messaging: WhatsApp, Telegram, Signal, Viber, Line, and more
- Password extraction: Retrieve saved passwords
- Social media monitoring: All major platforms including TikTok, Instagram, Snapchat
Considerations: Extremely invasive features may damage trust. Often requires jailbreaking (iOS) or rooting (Android), which compromises device security. Most expensive option.
Bark:
AI-powered monitoring focused on safety rather than constant surveillance:
- Content analysis: AI scans messages, posts, and emails for concerning content
- Alert-based system: Parents receive alerts only when potential issues are detected
- Privacy-respecting: Parents don’t see every message, only concerning ones
- Coverage: Monitors 30+ social media platforms and messaging apps
- Website filtering: Block inappropriate websites
- Screen time management: Set schedules and limits
- Location tracking: Check-in feature rather than constant tracking
Philosophy: Strikes a balance between safety and privacy, reducing parental intrusion while catching serious issues
Qustodio:
- Cross-platform monitoring (phones, tablets, computers)
- Screen time controls and scheduling
- App blocking and time limits
- Web filtering with category controls
- Call and SMS monitoring
- Social media monitoring (limited on iOS)
- Location tracking with geofencing
- Panic button for children to alert parents in emergencies
Net Nanny:
- Strong focus on content filtering
- Pornography blocking technology
- Real-time content filtering across apps and browsers
- Screen time management
- Location tracking
- YouTube monitoring
- Social media alerts
Never install monitoring software on devices you do not own — unauthorized installation violates federal wiretapping laws.
4. Router-Level Monitoring and Control
Home network controls affect all devices:
- Disney Circle: Hardware device managing all home network traffic
- Router parental controls: Many modern routers include built-in parental controls
- OpenDNS Family Shield: DNS-level filtering blocking inappropriate content
- Google WiFi: Family WiFi features with per-device controls
Security researchers consistently find that basic protective measures prevent over 80% of common surveillance attempts.
Advantages:
- Works on all devices using home network
- Cannot be bypassed by uninstalling apps
- Controls computers, tablets, gaming consoles, and phones uniformly
Apply these security measures consistently to protect your devices and accounts from unauthorized access.
Limitations:
- Only works on home network (not when child uses cellular data or other WiFi)
- Cannot monitor message content or social media activity
- VPN usage can bypass router controls
What About What You Can Monitor?

Monitoring capabilities depend on the tool used:
Location and Movement
- Real-time GPS location
- Location history showing where child has been
- Geofencing alerts when entering or leaving designated areas (home, school, friend’s house)
- Speed alerts for teenage drivers
- Check-in features allowing children to share location proactively
Never install monitoring software on devices you do not own — unauthorized installation violates federal wiretapping laws.
Communications
- SMS and MMS text messages (content and metadata)
- Messaging apps: WhatsApp, Telegram, Signal, Viber, Line
- Social media DMs: Instagram, Facebook, Snapchat, TikTok, Discord, Twitter/X
- Email content across multiple providers
- Call logs with duration, timestamps, and contact information
- Call recording (where legally permitted and technically possible)
- VoIP calls on platforms like WhatsApp, Skype, Discord
Security researchers consistently find that basic protective measures prevent over 80% of common surveillance attempts.
Social Media Activity
- Posts, comments, and likes on Instagram, TikTok, Snapchat, Facebook
- Stories and temporary content
- Friend lists and new connections
- Content shared or received
- Gaming communications (Discord, Xbox Live, PlayStation Network)
- YouTube viewing history and comments
Apply these security measures consistently to protect your devices and accounts from unauthorized access.
Device Usage
- Screen time totals and per-app breakdowns
- App installation and usage patterns
- Website browsing history across all browsers
- Searches performed
- Photos and videos stored on device
- Downloaded files
- Calendar events and notes
What About Ethical Considerations and Best Practices?

The Transparency Debate
Should children know they’re being monitored? Research and expert opinion strongly favor transparency:
Arguments for transparency:
- Builds trust rather than destroying it
- Teaches digital citizenship and accountability
- More effective behavior modification when children know they’re accountable
- Maintains parent-child relationship
- Models ethical behavior
- Prepares children for workplace monitoring they’ll encounter as adults
Never install monitoring software on devices you do not own — unauthorized installation violates federal wiretapping laws.
Arguments for covert monitoring:
- Children may hide concerning behavior if they know they’re watched
- Can discover issues child won’t voluntarily disclose
- Prevents child from circumventing monitoring
Expert consensus: The vast majority of child psychologists, parenting experts, and researchers recommend transparent monitoring. Covert surveillance should be reserved for situations involving serious safety concerns or suspected dangerous behavior.
Age-Appropriate Monitoring
Monitoring should evolve as children mature:
Ages 6-10 (Early Elementary):
- Extensive monitoring appropriate
- Limited device privileges
- Devices used in common areas
- Review content together regularly
- Focus on education about appropriate use
Security researchers consistently find that basic protective measures prevent over 80% of common surveillance attempts.
Ages 11-13 (Middle School):
- Continued monitoring with more independence
- Discuss specific concerns when they arise
- Allow some private communications while monitoring for safety
- Teach digital literacy and critical thinking
- Introduce concepts of online reputation
Apply these security measures consistently to protect your devices and accounts from unauthorized access.
Ages 14-16 (High School):
- Reduced monitoring as trust is earned
- Focus on location safety and major concerns
- Respect private conversations with friends
- Intervene only for serious issues
- Prepare for full independence
Never install monitoring software on devices you do not own — unauthorized installation violates federal wiretapping laws.
Ages 17-18 (Approaching Adulthood):
- Minimal monitoring
- Emphasize adult responsibilities
- Prepare to discontinue monitoring at age 18
- Maintain open communication rather than surveillance
Security researchers consistently find that basic protective measures prevent over 80% of common surveillance attempts.
What Should You Actually Monitor?
Not all monitoring capabilities should be used to their fullest extent:
Appropriate to monitor closely:
- Location for safety purposes
- Screen time and device usage hours
- App installations
- Concerning behavioral changes
- Contacts with unknown adults
- Exposure to inappropriate content
- Cyberbullying (as victim or perpetrator)
Apply these security measures consistently to protect your devices and accounts from unauthorized access.
Should be monitored more lightly:
- Communications with peers (spot-checking rather than reading everything)
- Social media activity (monitoring for concerning patterns rather than every post)
- Entertainment choices (unless clearly inappropriate)
Never install monitoring software on devices you do not own — unauthorized installation violates federal wiretapping laws.
Generally should not monitor:
- Private journals or notes (unless serious safety concern)
- Every detail of friendships and social dynamics
- Developing romantic relationships (unless safety concerns arise)
- Therapy communications or communications with school counselors
What About Alternatives and Supplements to Monitoring?

Monitoring is just one tool in comprehensive digital parenting:
Digital Citizenship Education
- Teach appropriate online behavior
- Discuss digital footprint and online reputation
- Explain privacy implications of sharing
- Model good digital behavior
- Discuss real-world consequences of online actions
Security researchers consistently find that basic protective measures prevent over 80% of common surveillance attempts.
Open Communication
- Regular check-ins about online experiences
- Create safe space for discussing concerning encounters
- Ask about friends and online communities
- Share your own experiences with technology challenges
- Avoid overreaction to minor issues
Apply these security measures consistently to protect your devices and accounts from unauthorized access.
Family Media Plan
- Establish clear family rules about device use
- Create device-free times and zones
- Set expectations about appropriate content
- Define consequences for rule violations
- Review and update rules as children grow
Never install monitoring software on devices you do not own — unauthorized installation violates federal wiretapping laws.
Gradual Independence
- Start with restricted devices and gradually increase privileges
- Use monitoring reduction as reward for responsible behavior
- Allow children to earn trust through demonstrated judgment
- Involve children in decisions about their digital life
What About Warning Signs That Might Warrant Increased Monitoring?

Sometimes circumstances justify enhanced oversight:
- Significant behavioral changes (withdrawal, mood swings, secrecy)
- Declining academic performance
- Changes in sleep patterns or appetite
- Loss of interest in previously enjoyed activities
- New friend groups the child is secretive about
- Evidence of cyberbullying (as victim or perpetrator)
- Suspected exposure to predatory behavior
- Self-harm or suicidal ideation
- Substance abuse concerns
- Contact with known dangerous individuals
In these situations, increased monitoring should be accompanied by professional help from therapists, counselors, or medical professionals.
What Should You Know About Technical Implementation Tips?
For iOS Devices
- Use Screen Time as primary tool (free and built-in)
- Create child Apple ID under Family Sharing
- Enable Ask to Buy for app purchases
- Share location through Find My
- Regularly review Screen Time reports together
- Consider additional app only if Screen Time is insufficient
Security researchers consistently find that basic protective measures prevent over 80% of common surveillance attempts.
For Android Devices
- Set up Family Link from the beginning
- Create supervised Google Account for child
- Configure appropriate content filters
- Set screen time limits and bedtime schedules
- Enable location tracking
- Review activity reports regularly
Apply these security measures consistently to protect your devices and accounts from unauthorized access.
General Tips
- Install monitoring tools before giving device to child
- Test all features to understand what you’ll see
- Keep monitoring app passwords secure and separate from device passwords
- Regularly check that monitoring tools are still functioning
- Update apps and operating systems to maintain compatibility
- Have backup monitoring method in case primary tool fails
“Digital security is a shared responsibility. Parents monitoring their children, employers securing company devices, and individuals protecting their own accounts all contribute to a safer ecosystem.”
Dr. Sarah Chen, Digital Forensics Expert, SANS Institute
What About Conclusion?
When additional monitoring is necessary, choose tools appropriate to your child’s age and specific concerns.
A parental monitoring app is a temporary tool for teaching judgment, not permanent surveillance.
The ultimate goal is raising children who navigate the digital world safely on their own.
Use a parental monitoring app to enhance your parenting, not replace trust and communication.
Frequently Asked Questions
In most cases, physical access is needed for 5-10 minutes to install monitoring software. Remote-only methods like iCloud monitoring require account credentials. True zero-click exploits exist but cost millions and target high-profile individuals — not average users.
Watch for unusual battery drain (20%+ faster than normal), unexplained data usage spikes, phone running hot during idle, and strange sounds during calls. Multiple signs appearing together warrant immediate investigation with a security scan.
A factory reset removes virtually all consumer-grade spyware. However, set up the device as new afterward — don't restore from backup, which might reinstall the monitoring software. Change all passwords from a different device after the reset.
No. Unauthorized wiretapping is illegal under federal law (18 U.S.C. 2511) regardless of your reasons. Exceptions exist only for law enforcement with warrants, parents monitoring minor children's devices, and employers on company-owned phones with employee notice.
Keep your phone physically secure — never leave it unattended or share your passcode. Enable biometric locks and auto-lock after 30 seconds. Keep your OS updated, only install apps from official stores, and use a VPN on public Wi-Fi.


