How To Wiretap a Phone If You Know The Number

Most people searching “wiretap a phone” expect a magic trick — enter a number, press a button, listen in. The reality is far more complicated and far less dramatic.
Scammers know this desperation well. They profit from parents worried about their kids and partners suspecting infidelity. Understanding what actually works saves you from wasting money on empty promises.
Unauthorized phone surveillance violates federal wiretapping laws including the U.S. Wiretap Act (18 U.S.C. § 2511) and similar statutes worldwide. Only monitor devices you legally.
Can You Really Wiretap a Phone With Just the Number?
Honest answer: it is extremely limited and nearly impossible for ordinary people. SS7 vulnerabilities exist in older telecom networks, but exploiting them requires sophisticated equipment and insider access.
A 2023 report from the European Union Agency for Cybersecurity found that 90% of “remote wiretap” services advertised online were confirmed scams collecting payment data.
Telecom carriers guard call data behind multiple security layers. Without a court order or direct cooperation from the carrier, no one can wiretap a phone or listen to live conversations from a number alone.
Parents searching for answers often fall for these promises out of genuine concern. Understanding the real technical limits helps you avoid wasting money and instead choose safe, legal options.
The bottom line is clear: you cannot wiretap a phone using only a number. Anyone promising otherwise is either lying or selling a scam product designed to steal your money.
“The most effective security measures are often the simplest: strong unique passwords, two-factor authentication, and keeping your software updated. Most breaches exploit basic oversights, not sophisticated vulnerabilities.”
Alex Rivera, CEH, OSCP
What Can You Actually Do With a Phone Number?
A phone number does give you some investigative starting points. None of them qualify as wiretapping, but they provide useful context about unknown callers.
Use Truecaller or WhitePages to identify unknown numbers before deciding whether to block or investigate further.
These legitimate alternatives accomplish far more than any remote wiretapping attempt through the number alone. They provide real-time data you can actually trust and act on.
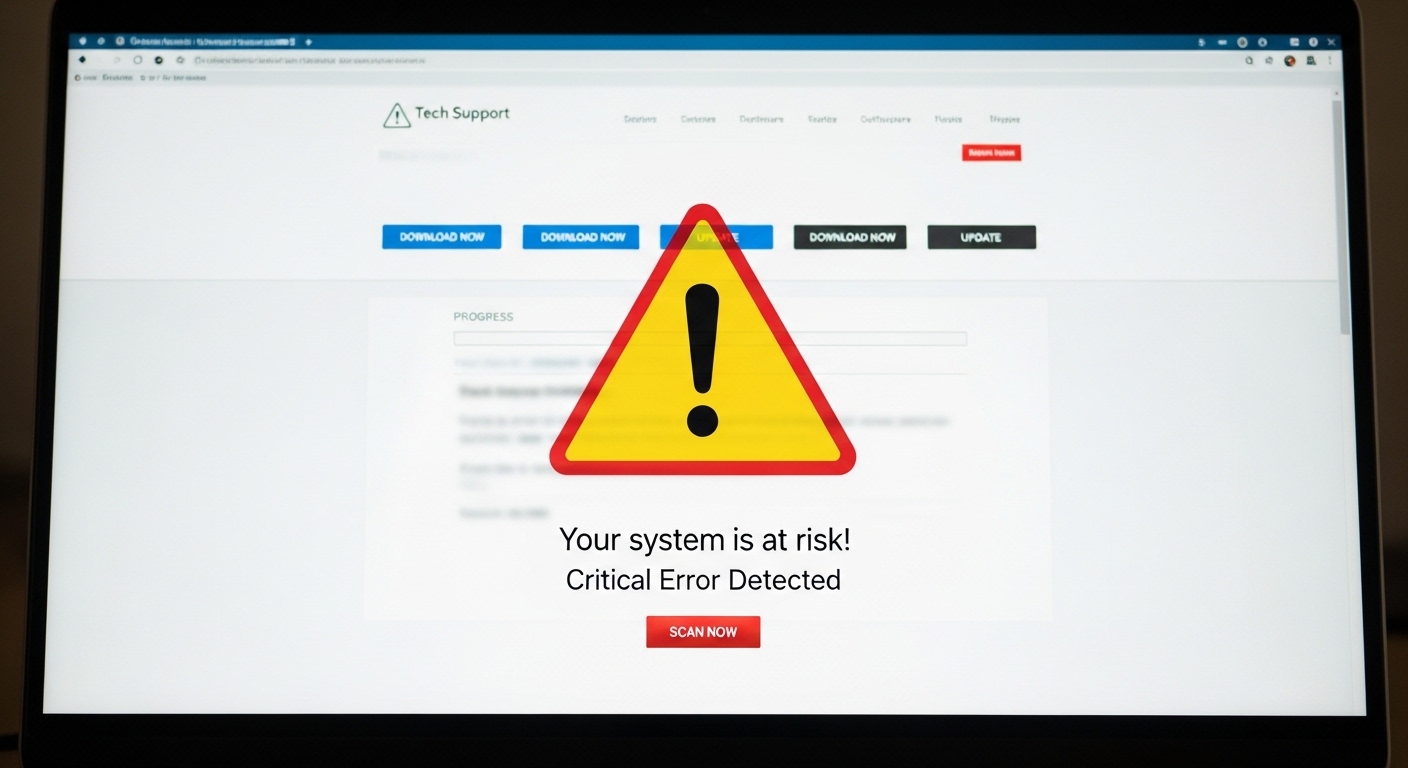
What About Why “Free Phone Wiretap” Services Are Scams?
Every website offering to wiretap a phone remotely for free is a scam. They cannot deliver what they promise because it violates basic technical realities of modern cellular networks.
These sites collect your payment information or personal details, then vanish. Some install malware on your own device while pretending to scan the target phone. Others steal credit card numbers through fake checkout pages.
Never enter payment details on any site claiming to wiretap a phone remotely. These services are confirmed scams that steal financial data and install malware.
Always verify monitoring services through independent review sites like PCMag or TechRadar. Check for a physical company address, real customer support channels, and transparent refund policies before purchasing anything.
How Phone Wiretapping Actually Works for Law Enforcement?
Law enforcement can legally wiretap a phone only after obtaining a court order. The process involves judges, prosecutors, and strict oversight at every step.
In the United States, carriers enable lawful intercept using CALEA protocols to route calls and messages to authorized agencies. This system is heavily audited and restricted to serious criminal investigations.
The U.S. Courts reported approximately 2,700 authorized wiretap orders in recent years, with narcotics cases accounting for over 75% of all approved intercepts.
Regular citizens have zero access to these law enforcement tools. The gap between law enforcement capabilities and what a civilian can legally accomplish is enormous and intentional.
What About Legitimate Phone Monitoring Alternatives?
Responsible parents can monitor their children’s devices using approved apps installed with consent. These tools provide real visibility into phone activity without attempting to wiretap a phone illegally.
Hoverwatch — Best for Stealth Android Monitoring
Hoverwatch stands out as a legitimate monitoring solution designed specifically for parents. It requires one-time physical access to install but then runs completely hidden in the background.
The app tracks GPS location, call logs, text messages, and social media activity on WhatsApp and Instagram.
Screenshots and keystroke logs give deeper insight without constant manual checking. It provides everything parents want when they search for ways to wiretap a phone — but through legal means.
Install Hoverwatch once on your child’s Android device for continuous stealth monitoring of calls, messages, location, and social media activity.
mSpy and FlexiSPY
 mSpy offers iCloud-based monitoring for iPhones without jailbreaking. You only need the child’s Apple ID credentials for remote setup. It tracks messages, browsing history, app usage, and location through iCloud sync.
mSpy offers iCloud-based monitoring for iPhones without jailbreaking. You only need the child’s Apple ID credentials for remote setup. It tracks messages, browsing history, app usage, and location through iCloud sync. FlexiSPY provides actual call recording — the feature closest to traditional wiretapping done legally. It captures both sides of phone conversations after installation and includes ambient recording capabilities.
FlexiSPY provides actual call recording — the feature closest to traditional wiretapping done legally. It captures both sides of phone conversations after installation and includes ambient recording capabilities.| App | Platforms | Key Features | Setup Method | Stealth Level | Best For |
|---|---|---|---|---|---|
| Hoverwatch | Android (primary) | GPS, calls, messages, social media screenshots | Physical access once | Very high | Stealth Android monitoring |
| mSpy | iOS and Android | iCloud sync, location, browsing, apps | Credentials or physical | High | iPhone parents |
| FlexiSPY | iOS and Android | Call recording, ambient listen, keystrokes | Physical access | High | Advanced call insights |
Use this comparison to identify the option that matches your requirements.
How Do You Tell If Your Phone Is Being Wiretapped?
Most phones show subtle signs when spyware is active. Professional-grade tools hide better, but consumer spyware almost always leaves traces you can spot.
If someone managed to wiretap a phone through installed spyware, certain telltale signs appear. Strange noises during calls, rapid battery drain, or unexpected data spikes often point to monitoring apps running in the background.
Your phone may heat up without reason or restart randomly during idle periods. Unfamiliar apps appearing in your settings menu is another common indicator.
Mobile security firm Lookout found that devices with spyware installed consume 30-50% more battery and use up to 3x more background data than clean phones.
If you notice these patterns, run a trusted security scan immediately. Learn more about detection methods in our guide on how to detect phone tracking.
How Do You Protect Your Phone From Wiretapping?
Strong daily habits keep your phone safe from unauthorized monitoring. These practical steps block the most common surveillance threats facing ordinary users.
Use encrypted calling apps like Signal for sensitive conversations. Keep your operating system updated and never click suspicious links from unknown senders. Regularly review installed apps and remove anything unfamiliar.
Enable two-factor authentication on every account, use Signal for private calls, and check your installed apps list weekly for anything suspicious.
A reputable VPN adds protection when using public Wi-Fi networks at coffee shops and airports. Physical access remains the biggest risk vector, so never leave your phone unattended around people you do not fully trust.
[colonizator_col]
Consider dedicated security apps like Malwarebytes or Bitdefender Mobile that actively detect spyware. These scan for known monitoring software signatures and alert you to suspicious background processes.
Anyone attempting phone surveillance typically needs physical access first. Protecting that physical access point closes the biggest vulnerability.
You might also want to learn how bluetooth wiretapping works as another attack vector to guard against.
[/colonizator_col]
[/colonizator_wrap]
“Digital security is a shared responsibility. Parents monitoring their children, employers securing company devices, and individuals protecting their own accounts all contribute to a safer ecosystem.”
Dr. Sarah Chen, Digital Forensics Expert, SANS Institute
Final Thoughts
Attempting to wiretap a phone with just a number is a myth that scammers exploit ruthlessly. Real monitoring requires proper device access and legal tools that respect privacy laws.
Parents who combine open communication with legitimate apps like Hoverwatch protect their children effectively without crossing legal boundaries. Stay informed about real threats, ignore impossible promises, and choose methods backed by actual technology.
Frequently Asked Questions
No, that is completely false. Modern cellular networks do not allow anyone to activate surveillance through a simple phone call. The person telling you this is either misinformed or trying to sell you a fake service. If you are genuinely worried about monitoring, check your installed apps and run a security scan instead.
Yes, but only with a judge-signed warrant based on real evidence of serious criminal activity. Carriers cooperate under strict CALEA regulations and everything gets audited. You would not know during an active investigation, but this process is reserved for major cases — not random surveillance of ordinary people.
Almost certainly not. Clicking and static come from poor signal strength, network congestion, or a damaged speaker. Modern wiretapping tools — both legal and illegal — are completely silent and leave no audible trace. If it keeps bothering you, test with a different phone on the same network to rule out hardware issues.
There is no magic code that reliably detects spyware or wiretaps. Codes like *#21# only show call forwarding settings, which is not the same thing at all. The only real way to check is reviewing your installed apps, examining battery and data usage patterns, and running antivirus software from a trusted provider like Malwarebytes.
End-to-end encryption in Signal and WhatsApp blocks carriers and most third parties from intercepting your messages or calls in transit. However, if spyware is already installed directly on your device, it can capture screen content before encryption kicks in. Keep your phone clean of suspicious apps and you are well protected against most realistic threats.