Modern Ways To Wiretap One’s Mobile Phone

Modern phone wiretapping has evolved far beyond physical phone line taps — today’s surveillance operates entirely through software, often invisible to the device owner.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
While brilliant minds continuously develop more sophisticated solutions for wiretapping cell phones and intercepting communications, these same innovations paradoxically make surveillance more accessible to ordinary individuals.
Understanding modern cell phone wiretapping methods serves both as a security awareness tool and a cautionary tale about privacy in the digital age.
This information is for educational purposes only. Unauthorized access to someone else’s device or accounts is illegal. Use these methods only on devices you own or with proper legal authorization.
What Are The Evolution of Cell Phone Wiretapping?
When mobile phones were first invented, little consideration was given to cell phone wiretapping or intercepting conversations.
As technology advanced, so did the methods for monitoring mobile communications — for both legitimate and illegal purposes.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
However, as mobile technology evolved, so did surveillance capabilities. Today in 2026, a diverse array of methods exist for wiretapping cell phones, each with varying levels of sophistication, legality, and accessibility.

“The most effective security measures are often the simplest: strong unique passwords, two-factor authentication, and keeping your software updated. Most breaches exploit basic oversights, not sophisticated vulnerabilities.”
Alex Rivera, CEH, OSCP
What About Understanding Modern Cell Phone Wiretapping?
Before examining specific methods, it’s crucial to understand that wiretapping cell phones in 2026 encompasses far more than traditional phone call interception. Modern surveillance includes monitoring:
- Traditional cellular voice calls
- VoIP and internet-based calls (WhatsApp, Telegram, Signal, Discord, FaceTime)
- Text messages and multimedia messages (SMS, MMS)
- Messaging app conversations (WhatsApp, Telegram, Signal, iMessage, Discord)
- Social media communications (Instagram, TikTok, Facebook Messenger, Snapchat)
- Email correspondence
- Video calls and conferencing
- Location tracking
The distinction between traditional cell phone wiretapping and comprehensive device monitoring has become increasingly blurred as communications migrate from cellular networks to encrypted internet-based platforms.
What About Method 1: Surveillance Software Installation?
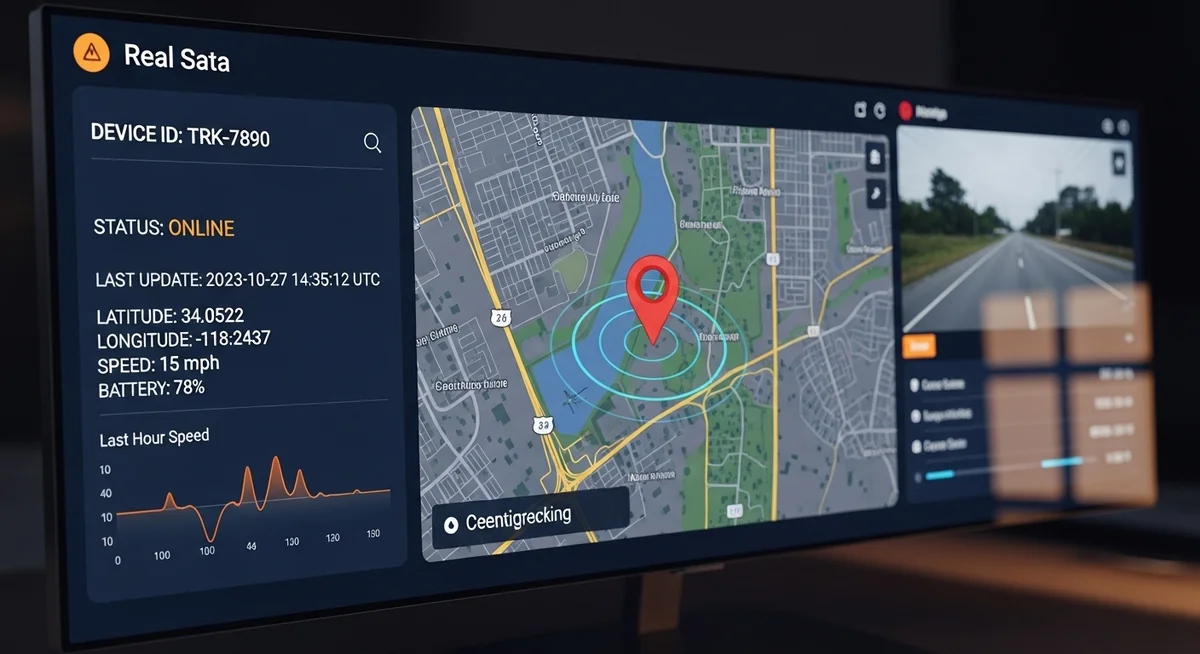
The most accessible modern cell phone wiretapping method involves installing specialized monitoring software directly on the target device. This approach represents a higher-tech evolution of traditional wiretapping and has become considerably easier to implement compared to older methods.
Installation requires brief physical access — typically 5-10 minutes while the device is unlocked. Hoverwatch offers the simplest setup process. Read our full review for details.
Software-based cell phone wiretapping covers all communication channels simultaneously — calls, messages, social media, GPS — through a single encrypted dashboard.
Platform-Specific Challenges

Both platforms continue adding protections, but determined monitoring software adapts to each new update.
What About Method 2: The Mobile-as-Bug Technique?

An innovative cell phone wiretapping approach treats the cell phone itself as a listening device without the owner’s knowledge.
How It Works
Certain specialized services allow you to dial a target cell phone number and listen to all ambient sounds in the device’s vicinity without the phone ringing, vibrating, or displaying any indication of the active connection.
This transforms the smartphone into an unwitting surveillance device.
Technical Implementation
This method typically requires:
- Subscription to specialized surveillance services
- Prior configuration or installation on the target device
- The phone remaining powered on
- Network connectivity
- Software that can answer calls silently and activate the microphone
Security researchers consistently find that basic protective measures prevent over 80% of common attacks.
Limitations
- Modern operating systems increasingly restrict background microphone access
- Users may notice unusual battery drain
- Data usage may reveal ongoing transmission
- Network logs show the active connection
- Only captures ambient audio, not the phone conversation itself
What About Method 3: Network-Level Interception?
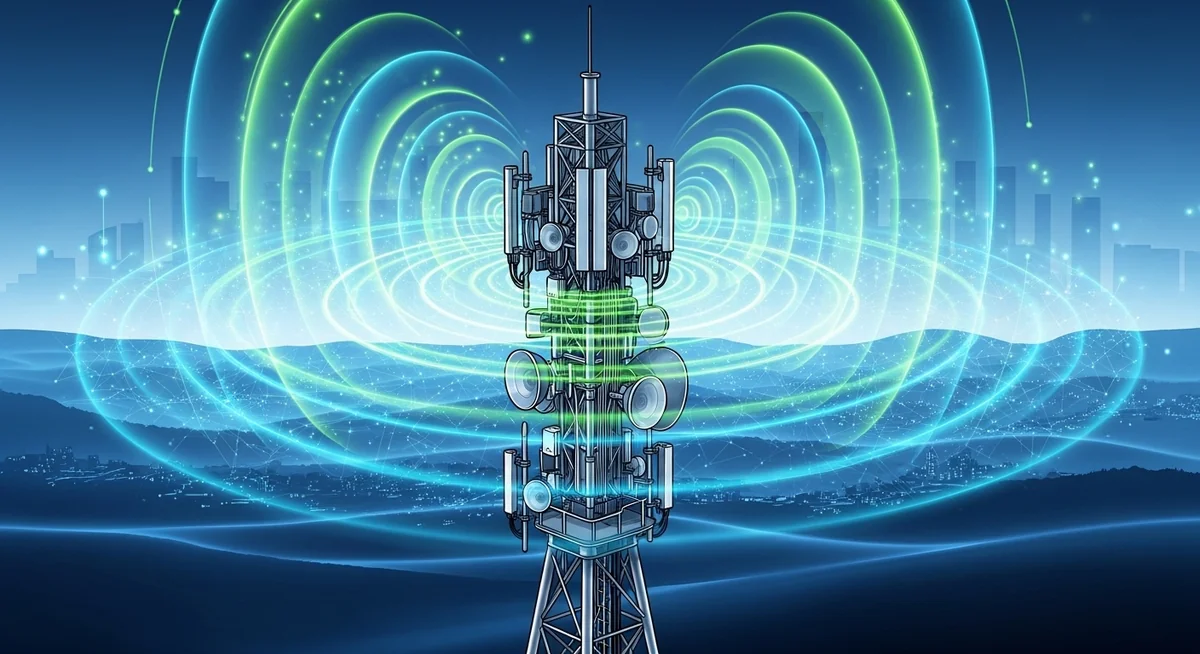
More sophisticated surveillance operates at the telecommunications network level rather than targeting individual devices.
IMSI Catchers (Stingrays)
IMSI catchers are devices that mimic legitimate cell towers, forcing nearby phones to connect to them. Once connected, these devices can:
- Intercept calls and text messages
- Track device locations
- Identify all devices in the area
- Monitor communications metadata
- Perform man-in-the-middle attacks
Apply these security measures consistently to minimize your exposure to common threats.
However, IMSI catchers:
- Are expensive (tens of thousands of dollars)
- Require technical expertise to operate
- Are illegal for civilian use in most jurisdictions
- Are primarily used by law enforcement and intelligence agencies
- Become less effective as networks upgrade to 5G with enhanced security
SS7 Protocol Exploitation
Signaling System No. 7 (SS7) represents a set of telephony signaling protocols used globally for setting up and managing phone calls. Despite being decades old, SS7 contains inherent security vulnerabilities that sophisticated attackers can exploit to:
- Intercept calls and text messages
- Track phone locations
- Bypass encryption
- Redirect calls
Never share your credentials with third-party services claiming to offer free access to accounts.
However, exploiting SS7:
- Requires expert-level telecommunications knowledge
- Demands access to the SS7 network (typically only available to telecom providers)
- Is illegal without authorization
- Is actively being patched by carriers
- Is primarily used by nation-state actors and advanced persistent threat groups
What About Method 4: Legal Wiretapping of Cell Phones by Authorities?

Government agencies and law enforcement can conduct lawful wiretapping of cell phones under specific circumstances.
Law Enforcement Access
Police, federal agencies, and intelligence services can wiretap phones when they obtain proper judicial authorization by:
- Demonstrating probable cause to a judge
- Obtaining a warrant or court order
- Working directly with telecommunications providers
- Following strict legal protocols and limitations
This legal framework ensures accountability while enabling legitimate criminal investigations and national security operations.
Carrier-Level Monitoring
Mobile network operators maintain capabilities to:
- Record call metadata (who called whom, when, duration)
- Store this information for periods ranging from months to years
- Provide data to law enforcement with proper legal authorization
- Track device locations through cell tower connections
You can request your own call records through official channels, but carriers will never provide another person’s records without legal authorization.
What About Modern Encryption and Its Impact?
The proliferation of end-to-end encrypted communication platforms has dramatically changed the landscape of wiretapping cell phones in 2026.
Encrypted Messaging Services
Apps like Signal, WhatsApp, Telegram (in secret chat mode), and iMessage use end-to-end encryption, meaning:
- Messages are encrypted on the sender’s device
- They remain encrypted in transit
- Only the recipient’s device can decrypt them
- Even the service provider cannot read message contents
- Network-level interception captures only encrypted data
Security researchers consistently find that basic protective measures prevent over 80% of common attacks.
Implications for Surveillance
End-to-end encryption forces surveillance efforts to target endpoints (the devices themselves) rather than the communication channel. This means:
- Network-level wiretapping becomes ineffective
- Device-level monitoring becomes necessary
- Physical or remote access to devices is required
- Social engineering and malware become primary attack vectors
What About Detection and Prevention?
Warning Signs of Cell Phone Wiretapping
Individuals concerned about potential cell phone wiretapping should watch for:
- Rapid battery drainage even when not actively using the phone
- Device heating up during idle periods
- Unusual data usage spikes
- Strange background noises during calls (clicking, echoes, static)
- Unexpected reboots or shutdowns
- Apps appearing that you didn’t install
- Sluggish performance or frequent freezing
- Difficulty shutting down the device
- Unexpected text messages with random characters
- Increased mobile data usage when not actively using apps
Protection Measures
To protect against wiretapping cell phones and safeguard your private communications:
- Keep your device physically secure; never leave it unattended and unlocked
- Use strong authentication (complex passwords, biometrics)
- Keep operating systems and apps updated with latest security patches
- Only install apps from official stores (Apple App Store, Google Play Store)
- Review app permissions regularly and revoke unnecessary access
- Install reputable mobile security software
- Use encrypted messaging apps (Signal, WhatsApp) instead of SMS
- Enable two-factor authentication on all accounts
- Avoid public Wi-Fi for sensitive communications
- Use VPN services to encrypt internet traffic
- Regularly check installed apps and remove unfamiliar ones
- Monitor battery usage to identify suspicious apps
- Factory reset if you suspect compromise
Choose the approach that best fits your specific situation and technical comfort level.
What Are The Arms Race Continues?

Advancing Protective Measures
Phone manufacturers become increasingly efficient at preventing wiretapping cell phones and related surveillance activities. Modern devices include:
- Hardware-level security features (Secure Enclave, Trusted Execution Environment)
- Machine learning-based anomaly detection
- Real-time privacy indicators showing camera/microphone usage
- Enhanced app sandboxing
- Verified boot processes
- Regular security patches addressing newly discovered vulnerabilities
Apply these security measures consistently to minimize your exposure to common threats.
Evolving Attack Methods
Simultaneously, surveillance technology continues advancing with:
- Zero-click exploits requiring no user interaction
- Supply chain attacks compromising devices before purchase
- AI-powered social engineering
- Quantum computing threatening current encryption methods
Never share your credentials with third-party services claiming to offer free access to accounts.
What About Legal and Ethical Implications?
Criminal Liability
Unauthorized wiretapping is illegal in virtually all jurisdictions and can result in:
- Federal felony charges (in the United States, violating the Wiretap Act)
- Significant prison sentences (often 5-20 years)
- Substantial fines (potentially hundreds of thousands of dollars)
- Civil lawsuits with significant damage awards
- Restraining orders and protective orders
- Loss of professional licenses
- Permanent criminal records affecting future employment
Security researchers consistently find that basic protective measures prevent over 80% of common attacks.
Ethical Considerations
Beyond legal concerns, wiretapping raises profound ethical questions:
- Fundamental violation of privacy and trust
- Treating people as objects to control rather than autonomous individuals
- Potential for abuse and manipulation
- Destruction of relationships when discovered
- Creating surveillance societies that erode fundamental freedoms
Apply these security measures consistently to minimize your exposure to common threats.
What About When Surveillance Might Be Justified?
Very limited circumstances exist where monitoring might be legally and ethically justified:
- Parents monitoring minor children’s devices (with age-appropriate transparency)
- Employers monitoring company-owned devices (with clear disclosure to employees)
- Law enforcement with proper judicial authorization
- Consensual monitoring between adults (such as shared family tracking)
Even in these scenarios, transparency and appropriate boundaries remain essential.
What About Legal Alternatives?
If you have legitimate concerns prompting interest in wiretapping cell phones, consider legal alternatives:
- Direct, honest communication about your concerns
- Relationship counseling or therapy
- Legal parental control apps (for minor children)
- Consulting with attorneys about legal evidence-gathering options
- Licensed private investigators operating within legal boundaries
- Mediation services for conflict resolution
“Digital security is a shared responsibility. Parents monitoring their children, employers securing company devices, and individuals protecting their own accounts all contribute to a safer ecosystem.”
Dr. Sarah Chen, Digital Forensics Expert, SANS Institute
What About Conclusion?
Modern cell phone wiretapping in 2026 encompasses a diverse array of methods ranging from sophisticated surveillance software to network-level interception and specialized hardware.
Technology continues advancing in both directions—phone producers develop ever more effective protections against wiretapping cell phones, while surveillance technologies become increasingly sophisticated and, in some cases, accessible.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
For individuals considering such surveillance, understand that attempting to wiretap cell phones without authorization requires valid justification given the enormous legal risks involved.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
Unauthorized surveillance constitutes serious criminal activity accompanied by potential imprisonment, massive fines, civil liability, and destroyed relationships. The temporary information gained through illegal wiretapping will never justify these life-altering consequences.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
The reality is that modern encryption, particularly on platforms like Signal, WhatsApp, Telegram, and iMessage, combined with improved security in iOS 10+ and Android 4.4+ devices, makes successful cell phone wiretapping increasingly difficult without sophisticated resources or device-level access.
Detection methods have also improved, meaning surveillance attempts are more likely to be discovered, resulting in both failed intelligence gathering and severe legal consequences.
For those concerned about their own privacy, implement comprehensive protection measures including strong device security, encrypted communications, vigilant monitoring for suspicious activity, and regular security updates.
The arms race between surveillance capabilities and privacy protections continues, but informed users who take security seriously can significantly reduce their vulnerability.
In a world where privacy becomes increasingly precious and constantly threatened, respect for others’ communications should remain a fundamental principle guiding our use of surveillance capabilities.
Frequently Asked Questions
In most cases, physical access is needed for 5-10 minutes to install monitoring software. Remote-only methods like iCloud monitoring require account credentials. True zero-click exploits exist but cost millions and target high-profile individuals — not average users.
Watch for unusual battery drain (20%+ faster than normal), unexplained data usage spikes, phone running hot during idle, and strange sounds during calls. Multiple signs appearing together warrant immediate investigation with a security scan.
A factory reset removes virtually all consumer-grade spyware. However, set up the device as new afterward — don't restore from backup, which might reinstall the monitoring software. Change all passwords from a different device after the reset.
No. Unauthorized wiretapping is illegal under federal law (18 U.S.C. 2511) regardless of your reasons. Exceptions exist only for law enforcement with warrants, parents monitoring minor children's devices, and employers on company-owned phones with employee notice.
Keep your phone physically secure — never leave it unattended or share your passcode. Enable biometric locks and auto-lock after 30 seconds. Keep your OS updated, only install apps from official stores, and use a VPN on public Wi-Fi.


