Is It Possible to Hack Snapchat
Snapchat accounts cannot be hacked through magic tools or free websites — but understanding how accounts actually get compromised helps you protect your family.
The platform’s temporary nature and visual focus make it particularly appealing to younger demographics and those seeking more private communication—though this same disappearing content is precisely what makes a Snapchat hack so damaging when it occurs.
Is a Snapchat hack really possible in 2026? With over 600 million active users, Snapchat remains a prime target for hackers. This guide explains real attack methods and how to protect your account.
Important: Hacking someone’s Snapchat without authorization is illegal. This guide is educational — helping you understand threats and protect your own account.
Why Do Hackers Target Snapchat Accounts?

In 2026, users share billions of photos and videos daily on Snapchat, making a Snapchat hack an extremely lucrative goal for various threat actors.
The combination of a massive user base and perceived privacy makes Snapchat uniquely attractive to different types of attackers.
Understanding why hackers target Snapchat is the first step toward protecting yourself and your family from these threats.
What Are the Most Common Snapchat Hacking Methods?

Despite Snapchat’s security measures, various methods exist for executing a Snapchat hack. Understanding these techniques helps users protect themselves and recognize attack attempts.
Phishing Attacks
Phishing represents one of the most effective methods to hack Snapchat accounts. Attackers create fake websites or pages that convincingly mimic Snapchat’s legitimate login interface. These fraudulent sites are designed to capture credentials when unsuspecting users attempt to log in.
Common phishing scenarios vary in sophistication, but all follow the same pattern — create urgency, then capture your credentials.
| Phishing Type | How It Looks | Red Flag |
|---|---|---|
| Account verification | Email claiming your account needs immediate action | Snapchat never emails login links |
| Premium features | Message promising free filters or increased snap score | No such feature exists |
| Security warning | Alert about suspension or violations | Real alerts appear in-app only |
| Profile viewers | Link to see “who viewed your profile” | Snapchat doesn’t offer this |
| Fake support | Customer support page asking for login | Support never asks for passwords |
| Cross-platform prompt | “Snapchat login required” on another site | Only log in at snapchat.com |
Once users enter their credentials on these fake pages, the information immediately transmits to attackers who can then access the legitimate account. Modern phishing sites in 2026 have become increasingly sophisticated, accurately replicating Snapchat’s branding, interface, and even security warnings.
“Phishing is still the number one way Snapchat accounts get compromised. The fake pages are nearly perfect now — the only reliable defense is to never click login links from messages. Always open Snapchat directly from your app.”
Alex Rivera, CEH, OSCP
Malware and Spyware
Malicious software represents another significant threat vector. Malware reaches Snapchat users through both online and physical channels.
Security researchers consistently find that basic protective measures prevent over 80% of common malware infections.
| Capability | Risk Level | How to Detect |
|---|---|---|
| Keylogging credentials | Critical | Check accessibility services for unknown apps |
| Screenshot capture | High | Unusual battery drain and data usage |
| Token interception | Critical | Unexpected login notifications from new devices |
| Activity monitoring | High | Device running hot during idle |
| Photo/video access | High | Check app permissions in Settings |
| Full account takeover | Critical | Password stops working, contacts report spam |
Modern mobile operating systems (iOS 10+ and Android 4.4+) include security features that make malware installation more difficult, but social engineering attacks that convince users to grant excessive permissions remain effective.
Social Engineering

Social engineering exploits human psychology rather than technical vulnerabilities. These attacks split into online and personal tactics.
This attack vector leverages trust and urgency to bypass technical security measures entirely. Trusting users may willingly provide their passwords to attackers without realizing they’re being manipulated.
Password Guessing and Brute Force Attacks
With information about users readily available across social media platforms like Instagram, TikTok, Facebook, and Twitter, attackers can attempt to guess passwords based on personal information. Common password patterns include:
| Pattern | Example | How Fast to Crack |
|---|---|---|
| Family/pet names | fluffy2024 | Minutes (dictionary attack) |
| Birthdays | sarah0315 | Hours (date combinations) |
| Sports teams | Lakers23! | Minutes (common patterns) |
| School + year | lincoln2022 | Hours (public info) |
| Keyboard patterns | qwerty12345 | Seconds (first guesses) |
| Letter substitutions | P@ssw0rd | Seconds (well-known trick) |
Credential Stuffing

Inexperienced users often reuse the same password across multiple platforms and services.
In 2026, countless databases containing billions of compromised credentials from various data breaches circulate online. Attackers use these databases to perform credential stuffing attacks, automatically testing stolen username/password combinations across many services including Snapchat.
Did you know: Over 15 billion stolen credentials circulate on the dark web. If you reuse passwords, checking haveibeenpwned.com reveals if your email appeared in a data breach.
Session Hijacking
Beyond stealing passwords, attackers may execute a Snapchat hack by hijacking active sessions. This can occur through:
Once an attacker obtains a valid session token, they can access the account without needing the password, potentially maintaining access even after the user changes their password if the session remains valid.
| Attack Method | Skill Required | Success Rate | Detection Difficulty |
|---|---|---|---|
| Phishing | Low | Medium-High | Easy (check URL) |
| Malware/Spyware | Medium | Medium | Medium (security scan) |
| Social Engineering | Low | Medium | Hard (no technical trace) |
| Credential Stuffing | Low | Low-Medium | Easy (2FA blocks it) |
| Session Hijacking | High | Low | Medium (login alerts) |
These precautions significantly reduce your risk of being compromised.
Why Are Third-Party Snapchat Apps Dangerous?

Many third-party services claim to offer enhanced Snapchat functionality—but using them is one of the most common ways to get your Snapchat hacked:
These services always require your Snapchat login credentials — the moment you enter them, attackers have full account access.
Additionally, using third-party apps violates Snapchat’s Terms of Service and can result in permanent account suspension.
Warning: Never enter your Snapchat password on any website except snapchat.com or in the official app. Every “free Snapchat tool” website is a credential harvester.
What Motivates Snapchat Hackers?

Hacking accounts—whether Snapchat or other platforms—represents a fascinating challenge for many cybercriminals, providing creative outlet and multiple motivations:
Testing Skills
Some hackers compromise accounts purely to demonstrate technical capabilities, treating it as an intellectual challenge rather than for personal gain. For these individuals, successfully bypassing security measures provides satisfaction and builds reputation in hacking communities.
Financial Gain
Many attackers seek monetary rewards through:
| Method | Estimated Revenue | Difficulty |
|---|---|---|
| Selling compromised accounts | $5–50 per account | Low |
| Blackmail with private content | $100–10,000+ | Medium |
| Advertising scam campaigns | $50–500 per campaign | Low |
| Stealing linked payment info | Varies widely | High |
| Phishing victim’s contacts | $10–100 per successful hit | Medium |
Never share your credentials with third-party services claiming to offer free access to accounts.
Personal Reasons
Some attacks stem from personal motivations including:
Stay vigilant and never trust third-party tools that promise features Snapchat does not officially offer.
How Does Snapchat Protect Your Account?

Snapchat has significantly enhanced its security measures against Snapchat hack attempts in response to previous breaches and ongoing threats:
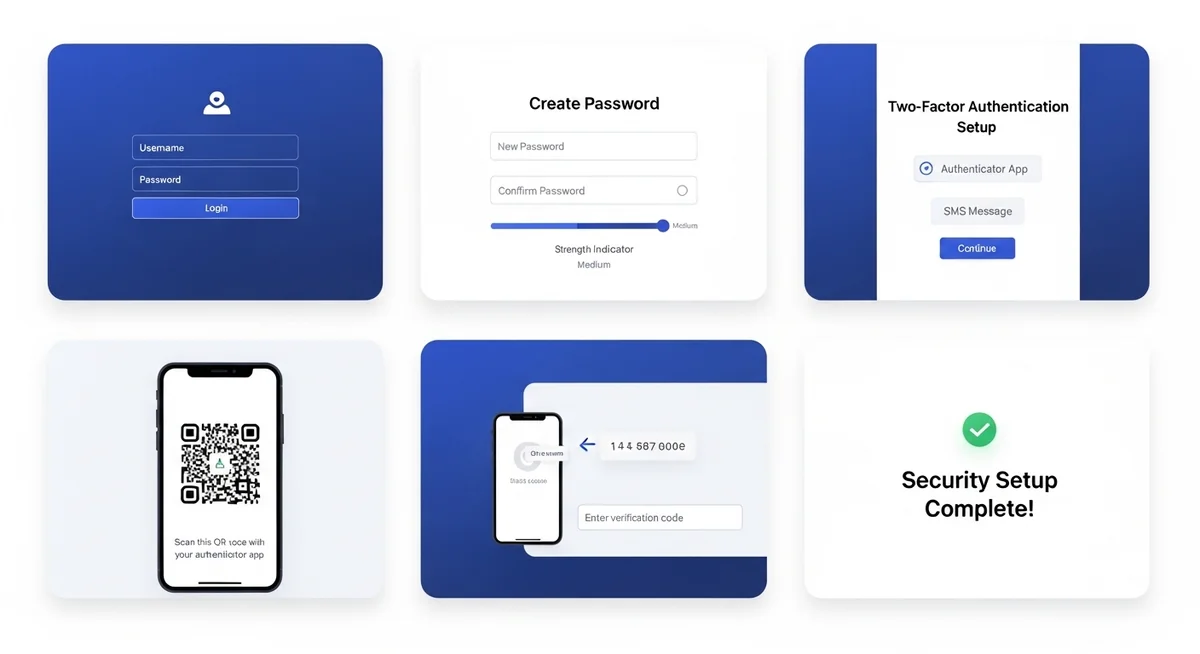
Two-Factor Authentication
Snapchat offers robust two-factor authentication options including:
- SMS verification codes
- Authentication apps (Google Authenticator, Authy)
- Biometric authentication on supported devices
Enabling 2FA substantially reduces account compromise risk, as attackers need both the password and the second factor to gain access.
Login Verification
Snapchat notifies users of login attempts from new devices or locations, allowing them to approve or deny access attempts. This helps detect unauthorized access attempts in real-time.
End-to-End Encryption

While not all Snapchat messages use end-to-end encryption, the platform has expanded its use of encryption for certain communications, making interception more difficult without compromising the device itself.
Security Alerts
Modern Snapchat accounts receive security alerts that help you catch unauthorized access early.
These protective features work best when combined with strong personal security habits.
How Can You Secure Your Snapchat Account?
Users can take multiple steps to secure their accounts and avoid becoming a Snapchat hack victim:
“The combination of a unique password and an authenticator app makes your Snapchat account virtually unhackable through remote attacks. The only remaining risk is physical access to your unlocked phone.”
Dr. Sarah Chen, Digital Forensics Expert, SANS Institute
Securing your Snapchat account requires action in four areas: authentication, behavior, device settings, and privacy configuration.
Beyond authentication and habits, your behavioral patterns online determine most of your risk exposure.
| Security Habit | Why It Matters | Difficulty |
|---|---|---|
| Use a password manager | Generates and stores unique passwords for every account | Easy (one-time setup) |
| Verify URLs before login | Blocks all phishing attempts at the source | Easy (check address bar) |
| Avoid third-party apps | Eliminates the #1 credential theft vector | Easy (just don’t install) |
| Check login notifications | Catches unauthorized access within minutes | Easy (read alerts) |
| Review connected apps monthly | Revokes access from forgotten or compromised services | Medium (2 minutes/month) |
| Log out on shared devices | Prevents session hijacking on public computers | Easy (one tap) |
Security researchers consistently find that basic protective measures prevent over 80% of common attacks.
Configuring these settings takes under five minutes and dramatically reduces your attack surface.
Quick security check: Open Snapchat Settings right now. Enable 2FA, check Login Verification, review connected apps, and turn on Ghost Mode. Takes 2 minutes.
Does Your Security on Other Platforms Affect Snapchat?

A Snapchat hack rarely happens in isolation—your overall security posture across platforms like Instagram, TikTok, Discord, Telegram, Signal, and WhatsApp all contribute to your risk level. Attackers often:
- Gather information from one platform to attack another
- Use compromised accounts on one service to phish contacts on others
- Leverage information from data breaches affecting multiple services
Maintaining strong security practices across all platforms enhances your overall protection.
How Valuable Is a Hacked Snapchat Account?

In the modern digital landscape, login credentials for social media accounts can be more valuable than traditional email access.
While email systems have developed extensive experience combating threats, and users spend less time in email interfaces, social networks like Snapchat, Instagram, TikTok, and Discord dominate users’ attention and trust.
Compromised Snapchat accounts sell for $5–50 each on dark web marketplaces, while accounts with large followings or linked payment methods command significantly higher prices.
Attackers choose the most accessible target. If your Snapchat account has weak security, it becomes the obvious entry point—potentially providing access to your entire digital life through linked accounts and saved information.
What Are the Legal Consequences of Hacking Snapchat?

Hacking someone’s Snapchat account without authorization is illegal in virtually all jurisdictions. Potential consequences include:
| Consequence | Severity | Example |
|---|---|---|
| Criminal prosecution | Felony | Computer Fraud and Abuse Act charges |
| Fines and imprisonment | Up to 10 years | Federal sentencing guidelines |
| Civil liability | $10,000–$1M+ | Damages, legal fees, settlements |
| Restraining orders | Ongoing | Court-ordered no-contact provisions |
| Criminal record | Permanent | Affects employment, housing, travel |
Serious: Even attempting to hack a Snapchat account can result in federal charges under the Computer Fraud and Abuse Act, with penalties up to 10 years imprisonment.
Final Thoughts
Every Snapchat hack exploits human behavior — reused passwords, phishing clicks, or weak authentication. A unique password plus an authenticator app blocks virtually all remote attacks.
For parents monitoring their child’s Snapchat, Hoverwatch captures messages and screenshots in stealth mode on devices you own — the legal and effective alternative to hacking.
Frequently Asked Questions
Yes, primarily through phishing links and credential stuffing from data breaches. Direct technical hacking is rare for regular users. The most common scenario: you click a fake login link or reuse a password that was exposed in a breach. Enable 2FA and use a unique password to block both attacks.
Almost certainly a phishing attempt. Snapchat sends security notifications through the app itself, not via email links or text messages. Never click links in these messages. Instead, open the Snapchat app directly and check Settings for any security alerts.
No. Every single one is a scam designed to steal YOUR credentials or install malware on YOUR device. There is no website that can retrieve someone's Snapchat password. If it sounds too easy, it's fake.
Signs include: login notifications from devices you don't recognize, friends reporting strange messages from your account, your password suddenly not working, or changes to your email or phone number you didn't make. Check Settings → My Data to review recent login activity.
If you're a minor and the phone belongs to your parent, yes — in most jurisdictions. Parents can install monitoring apps like Hoverwatch on devices they own. If you're over 18, they need your consent. The legality depends on device ownership and your age, not the app used.





Social networking websites and apps, such as Facebook, MySpace, Instagram, Viber, Tumblr, SnapChat, Ask.fm and Twitter have become incredibly popular in recent years.