How to Hack Instagram If You are Not a Hacker
No, you cannot truly hack Instagram account without technical expertise — but understanding how accounts get compromised helps you protect your family from the most common threats online.
As a parent, knowing how easy it is for someone to hack instagram account helps you protect your kids and yourself.
The real threats are closer to home than you think.
Unauthorized access to someone’s Instagram account violates the Computer Fraud and Abuse Act (CFAA) and similar laws worldwide. Parental monitoring of minors is legal with.
How Do Instagram Accounts Actually Get Compromised?

Over 80% of account compromises involve social engineering rather than technical exploits, according to cybersecurity researchers.
Phishing Pages and Fake Login Screens
Attackers create convincing fake Instagram login pages identical to the real app or website.
They send links via direct messages, emails, or fake “Instagram support” alerts claiming your account is at risk.
When your child enters their username and password, the scammers capture everything instantly.
The pages use similar logos, fonts, and even the official URL with slight misspellings.
Never click login links from messages or emails. Real Instagram never asks for credentials outside the official app.
Password Reset Exploitation
If someone gains access to your child’s linked email or phone number, they can trigger a password reset on Instagram.
They request the reset, receive the code, and lock you out in minutes.
No technical skills required — just knowing or guessing the recovery email. Once they control the email inbox, the Instagram account follows.
Always use a unique, strong password for email that isn’t reused anywhere else — it’s the master key to all linked accounts.
Public Wi-Fi Risks
Logging into Instagram on unsecured public Wi-Fi lets attackers intercept login sessions through man-in-the-middle tricks.
Your child’s phone connecting automatically to coffee shop Wi-Fi is a common entry point.
A quick fix is using a VPN on family devices. It encrypts everything and stops session hijacking cold.
Credential Stuffing From Data Breaches
Credential stuffing takes usernames and passwords stolen from other sites and tries them on Instagram.
Since most people reuse passwords, one breach elsewhere can hack instagram account here.
Billions of stolen credentials circulate on the dark web, and automated tools can test thousands of combinations per minute against Instagram.
“The most effective security measures are often the simplest: strong unique passwords, two-factor authentication, and keeping your software updated. Most breaches exploit basic oversights, not sophisticated vulnerabilities.”
Alex Rivera, CEH, OSCP
What About Why “Free Instagram Hack” Websites Are Always Scams?

Those sites that promise to hack any Instagram account for free are designed to trick you, not help you.
They load up flashy landing pages with big “Hack Now” buttons and fake testimonials.
The moment you enter a target username, the real work begins — for them, not you.
You’ll see animated progress bars slowly filling up or looping “processing database” screens with spinning icons.
These are just JavaScript tricks to keep you watching while the site grabs your data in the background. Nothing is actually being hacked.
These sites steal your data, not someone else’s account. Never enter your password or phone number on any “free hack” tool.
It asks for your Instagram username and password right away.
Many also route you through long surveys that collect your phone number, email, and sometimes payment details to “unlock” the next step.
The surveys are the real moneymaker.
Scammers plug into CPA networks that pay them cash for every completed form.
You think you’re one survey away from the hack — they’re just collecting your info to sell or use later.
Real Red Flags You Should Spot Instantly
- No HTTPS padlock in the browser bar
- Domain names like instahacktool.xyz, freeigcrack.online, or anything with random numbers and hyphens
- The site asks for your own Instagram password or 2FA code
If your kid already used one of these sites, have them change their Instagram password immediately from the official Instagram app.
Check the linked email and phone number.
Also see our guide on Gmail security for any new logins or recovery attempts.
Enable two-factor authentication and scan their device for malware if they downloaded anything.
What About Legitimate Parental Monitoring Solutions?

Parents who want to monitor their children’s Instagram activity don’t need shady tools.
Legal, ethical parental monitoring apps give you full visibility into DMs, posts, and activity while staying completely transparent.
Hoverwatch
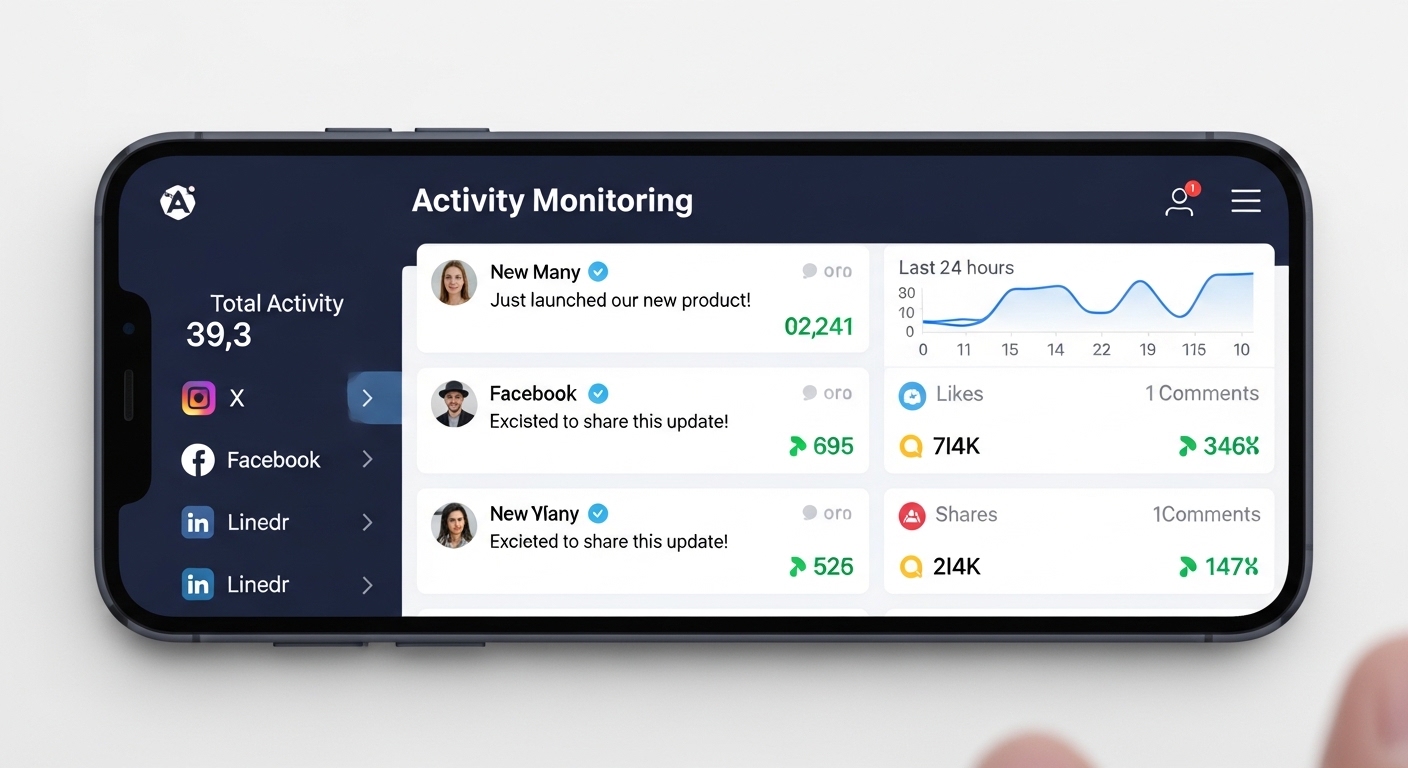
Hoverwatch stands out as the top recommendation for parents. It delivers screenshots of social media activity, including full Instagram direct messages and shared links, all in stealth mode.

The app runs completely invisible on the child’s Android device with no icons or notifications. All data goes to a secure web dashboard you access from any browser.
Beyond Instagram, Hoverwatch tracks GPS location in real time, call history, and internet activity.
Setup takes minutes — just install once with physical access to the phone.
Pricing starts at $29.95 per month for one device, with a 3-day free trial so you can test everything risk-free.
mSpy
mSpy offers excellent Instagram DM monitoring, capturing messages, photos, videos, and even deleted content in many cases.
It includes a built-in keylogger and screen recorder for complete visibility.
Pricing is flexible: one month at $48.99, three months at $27.99/month, or twelve months at just $11.66/month.
It works on both iOS and Android, making it ideal for mixed-device families.
FlexiSPY
FlexiSPY provides the most advanced Instagram monitoring with direct message capture plus call recording and ambient listening features.
It goes beyond screenshots to record actual voice calls if needed.
Pricing starts higher with the Lite plan around $49.95/month and climbs for Premium and Extreme tiers.
Best for parents who need maximum detail and are willing to pay for premium features.
| App | Instagram Monitoring | Stealth Mode | Starting Price | Platforms |
|---|---|---|---|---|
| Hoverwatch | Screenshots of DMs, stories, and activity | Yes — fully invisible | $29.95/month | Android, Windows/Mac dashboard |
| mSpy | Full DMs, media, deleted messages | Yes | $11.66/month (annual) | iOS and Android |
| FlexiSPY | Advanced DMs plus call & ambient recording | Yes | $49.95/month (Lite) | iOS and Android |
Use this comparison to identify the option that matches your requirements.
How Do You Protect Your Instagram Account?

Strong protection starts with simple habits anyone can adopt today. These steps stop the vast majority of attempts to hack instagram account before they succeed.
Enable Two-Factor Authentication
Two-factor authentication adds a second layer that stops hackers even if they steal the password.
Open Instagram, go to Settings > Accounts Center > Password and security > Two-factor authentication.
Choose an authenticator app like Google Authenticator instead of SMS — it blocks almost every common attack and takes just two minutes to set up.
Review Login Activity Regularly
Check where your account is logged in every month. Go to Settings > Accounts Center > Password and security > Where you’re logged in.
Look for unfamiliar devices or locations — log them out immediately. Make it a family routine on the first Sunday of every month.
Use Unique Passwords
Never reuse the same password across sites. A single data breach elsewhere can let attackers hack instagram account through credential stuffing.
Use a password manager like Bitwarden or your phone’s built-in one to generate and store strong, unique passwords. Change your Instagram password every few months.
Remove Suspicious Third-Party Apps
Go to Settings > Security > Apps and websites to see everything connected to your Instagram.
Revoke access for any app you don’t recognize or no longer use.
What About What to Do If Your Account Has Been Compromised?

Act in the first 15 minutes.
Change the password on the email address tied to your Instagram account. Then go through every other app or site that uses the same password and update those immediately.
Log out of Instagram on all devices if you can still get in.
Speed matters here — the longer a hacker has control, the harder recovery becomes.
Change your email password first, then Instagram. Email is the master key — secure it before anything else.
Instagram’s Official Recovery Steps
Open the Instagram app or website and tap “Get help logging in” on the login screen.
Choose the “My account was hacked” option and fill out the form with your old username, linked email or phone, and any details you remember.

Instagram will usually ask for a short video selfie where you turn your head or make specific movements to prove it’s you. Submit the request and wait — most users hear back within 3-7 business days.
If recovery fails after two attempts, report the hacked account again through the same form. Follow up via Facebook or Meta support using your linked business account if you have one.
Avoid third-party “recovery services” that ask for payment — they’re the same scams in different packaging.
Prevent It From Happening Again
- Use a completely new, strong password you haven’t used anywhere else
- Review and remove any suspicious app permissions in your Instagram settings
- Turn on two-factor authentication with an authenticator app, not SMS
Common mistake: creating a brand-new account right away and losing all your followers and content.
Another big one is searching for “Instagram recovery help” and handing your details to yet another scam service.
Stick to Instagram’s own tools and you’ll get your account back faster.
“Digital security is a shared responsibility. Parents monitoring their children, employers securing company devices, and individuals protecting their own accounts all contribute to a safer ecosystem.”
Dr. Sarah Chen, Digital Forensics Expert, SANS Institute
Final Thoughts
Understanding how easy it is for someone to hack instagram account takes the mystery out of online safety.
Focus on education, strong habits, and legitimate tools like Hoverwatch when you need visibility into your kids’ activity.
Teach these lessons early, use the right monitoring solutions when appropriate, and model good security yourself.
Knowing how people hack Instagram account helps you stay safe.
That combination keeps the real threats away far more effectively than any “hack” tool ever could.
Frequently Asked Questions
Yes, Instagram has a dedicated recovery process for exactly this. Use the "Get help logging in" option and select the hacked account form — you'll need to submit a government-issued ID and a selfie video holding a code they provide. Recovery usually takes 3-7 days if you can prove ownership. Don't waste time with third-party "recovery services" — they're all scams.
Nope, a username alone isn't enough to get into your account. They still need your password, a session token, or control of your recovery email or phone. What a username does help with is targeting you for phishing or password reset attempts — but those still require more steps to actually work.
Not a single one. Every "free hack" site is either stealing your information, making you complete surveys so the scammers get paid, or installing malware on your device. Real account access requires device-level monitoring software or social engineering — never a random website. If it sounds too easy, it's definitely a scam.
No, Hoverwatch runs in complete stealth mode — no visible icons, no notifications, and it doesn't show up in the app list. Your child won't know it's installed unless you tell them. Everything gets sent quietly to your private web dashboard that you can check from any browser.
Strong passwords only protect against guessing and brute force. Most hacks happen through phishing (you entered your password on a fake page), credential stuffing from breaches on other sites, or session hijacking on public Wi-Fi. That's why 2FA and unique passwords across all your accounts are essential — a strong password alone just isn't enough anymore.