Top Methods Of Hacking Twitter

Anyone can hack Twitter account through phishing, keyloggers, or credential stuffing — understanding these methods is the best defense against them.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
The platform’s role in news dissemination, political discourse, and public communication makes accounts valuable targets for various reasons. However, understanding how to hack a Twitter account—or even attempting it—carries serious legal, ethical, and technical implications that must be understood before proceeding.
This information is for educational purposes only. Unauthorized access to someone else’s device or accounts is illegal. Use these methods only on devices you own or with proper legal authorization.
What About Understanding the Challenge of Hacking a Twitter Account?

Hacking a Twitter account—or gaining any unauthorized access to the platform—is no simple task.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
The platform has invested billions in security infrastructure since its inception, employing some of the world’s leading cybersecurity experts. The security measures protecting individual accounts also protect the platform’s extensive databases containing sensitive user information.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
Whether you’re attempting to hack a Twitter account belonging to your ex-partner, a business competitor’s profile, or a celebrity’s feed, the technical challenges remain substantial. More importantly, the legal consequences can be severe, including criminal charges, fines, and imprisonment.
“The most effective security measures are often the simplest: strong unique passwords, two-factor authentication, and keeping your software updated. Most breaches exploit basic oversights, not sophisticated vulnerabilities.”
Alex Rivera, CEH, OSCP
Why the Desire to Hack Twitter Accounts?

Choose the approach that best fits your specific situation and security needs.
What Are The Reality of Relationship Spying?

If you’re considering hacking a spouse’s or partner’s Twitter account, understand the implications beyond technical and legal concerns.
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
If you discover evidence of wrongdoing, that evidence may be inadmissible in legal proceedings like divorce cases because it was obtained illegally. If you find nothing incriminating, you’ve still damaged your relationship and violated someone’s privacy.
Consider these alternatives before attempting to hack a Twitter account:
- Direct conversation about your concerns
- Couples counseling to address trust issues
- Consulting with a therapist about your suspicions
- If divorce seems inevitable, consulting an attorney about proper evidence gathering
What Are the Top Methods Used to Hack a Twitter Account?

Understanding how attackers hack Twitter account credentials helps you protect yourself. Hoverwatch monitors social media including Twitter — see our full review.
Keyloggers record every keystroke including Twitter passwords. They remain one of the oldest techniques used to hack a Twitter account.
How it works:
- Obtain physical access to the target’s device (computer, tablet, or smartphone)
- Install keylogger software (5-15 minutes of unattended access required)
- Configure the software to transmit captured data to your email or control panel
- Wait for the target to log into Twitter
- Retrieve the captured username and password
- Use the credentials to access the account from your own device
Never enter your credentials on third-party websites promising free account access. These sites harvest your own login data instead.
Challenges and limitations:
- Requires physical device access for installation
- Modern antivirus software detects most keyloggers
- Operating systems now warn users before granting necessary permissions
- Two-factor authentication prevents access even with correct passwords
- Suspicious login attempts trigger security alerts to the account owner
- Many common approach when attempting to hack a Twitter account without direct device access.Legal status: Installing spyware on devices you don’t own is illegal under computer fraud and abuse laws in most countries. Penalties include substantial fines and imprisonment.Phishing involves tricking someone into clicking a malicious link that either steals their credentials directly or installs spyware—a common approach when attempting to hack a Twitter account without direct device access.
Common phishing techniques:
- Fake security alerts claiming “Your Twitter account has been compromised – click here to verify”
- Impersonating Twitter support with emails about policy violations
- Creating fake login pages that appear identical to Twitter’s legitimate site
- Sending links disguised as interesting content (videos, articles, images)
- Using URL shorteners to hide suspicious destination addresses
According to cybersecurity researchers, over 80% of account compromises stem from reused passwords and social engineering rather than technical exploits.
Modern protections against phishing:
- Email providers filter most phishing attempts before they reach inboxes
- Browsers display warnings when accessing known phishing sites
- Twitter never asks for passwords via email or direct message
- User awareness of phishing has increased significantly since 2019
- Multi-factor authentication prevents access even if passwords are stolen
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
Creating convincing phishing requires:
- Web development skills to clone Twitter’s login page
- Server infrastructure to host the fake site
- Understanding of how to harvest and transmit credentials
- Social engineering skills to craft convincing messages
- Methods to avoid detection by security systems
3. Email Account Compromise
Every Twitter account is linked to an email address or phone number. Gaining access to the associated email account provides a direct pathway to hack a Twitter account through password reset mechanisms.
The process:
- Identify the email address associated with the target’s Twitter account
- Compromise the email account using keyloggers, phishing, or password guessing
- Navigate to Twitter’s password reset page
- Request a password reset link
- Access the reset link from the compromised email
- Set a new password for the Twitter account
- Delete the password reset notification to avoid detection
Never enter your credentials on third-party websites promising free account access. These sites harvest your own login data instead.
Challenges:
- Email accounts typically have strong security including two-factor authentication
- Password reset notifications are also sent to registered phone numbers
- Twitter monitors for suspicious password changes and may require additional verification
- The account owner receives multiple notifications about the password change
- Modern email providers log all access, creating a digital trail
4. Browser Saved Password Exploitation
Many users allow their web browsers to save login credentials for convenience. If you can access someone’s unlocked computer or device, you may be able to view these stored passwords and use them to hack a Twitter account directly.
Accessing saved passwords:
Chrome: Settings → Passwords → View saved passwords (requires device password on most systems)Firefox: Settings → Privacy & Security → Saved Logins (requires master password if configured)Safari: Preferences → Passwords (requires device password)
Edge: Settings → Passwords (requires device password)
Limitations:
- Requires physical access to an unlocked device
- Most browsers now require device password to view saved credentials
- Accessing someone else’s device without permission is illegal
- The victim will likely notice you using their computer
- Two-factor authentication still prevents account access
5. Social Engineering and Password Guessing
If you know the target personally, you might attempt to hack a Twitter account by guessing their password based on personal information.
Common password patterns:
- Pet names with numbers (Fluffy2019)
- Significant dates (birthdays, anniversaries)
- Children’s or spouse’s names
- Favorite sports teams or celebrities
- Simple patterns (Password123, qwerty123)
- Variations of the service name (Twitter2026)
According to cybersecurity researchers, over 80% of account compromises stem from reused passwords and social engineering rather than technical exploits.
Reality check:
- Twitter implements rate limiting, locking accounts after several failed login attempts
- Security-conscious users employ password managers generating random, complex passwords
- Failed login attempts generate security alerts
- IP addresses of failed attempts are logged
- Success rate is extremely low
6. SIM Swapping for 2FA Bypass
Some accounts use SMS-based two-factor authentication. SIM swapping involves convincing a mobile carrier to transfer the target’s phone number to a SIM card you control, providing a pathway to hack a Twitter account protected by SMS-based 2FA.
The attack process:
- Gather personal information about the target (address, social security number, etc.)
- Contact the mobile carrier impersonating the target or bribing an employee
- Request the phone number be ported to a new SIM card
- Use the hijacked number to receive 2FA codes
- Access accounts protected by SMS-based 2FA
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
Developments since 2019:
- Carriers have significantly strengthened identity verification procedures
- High-profile SIM swapping attacks led to major prosecutions
- Twitter/X now recommends authenticator apps over SMS for 2FA
- Law enforcement treats SIM swapping as serious fraud
- Carriers implement additional PINs and verification methods
7. Database Breaches and Credential Stuffing
When services experience data breaches, user credentials are often stolen and sold on dark web markets. Attackers purchase these databases and attempt to use the credentials to hack Twitter accounts and other services.
How credential stuffing works:
- Obtain username/password combinations from breached databases
- Use automated tools to test these credentials on Twitter
- Many users reuse passwords across multiple services
- Successfully matching credentials grant account access
Never enter your credentials on third-party websites promising free account access. These sites harvest your own login data instead.
Twitter’s defenses:
- Advanced bot detection prevents automated login attempts
- Machine learning identifies credential stuffing patterns
- Suspicious login attempts trigger additional verification
- Rate limiting slows down automated attacks
- IP reputation systems block known attack sources
What About Twitter’s Evolving Security Measures?
Since 2019, Twitter/X has significantly enhanced security features specifically designed to prevent anyone from successfully hacking a Twitter account:
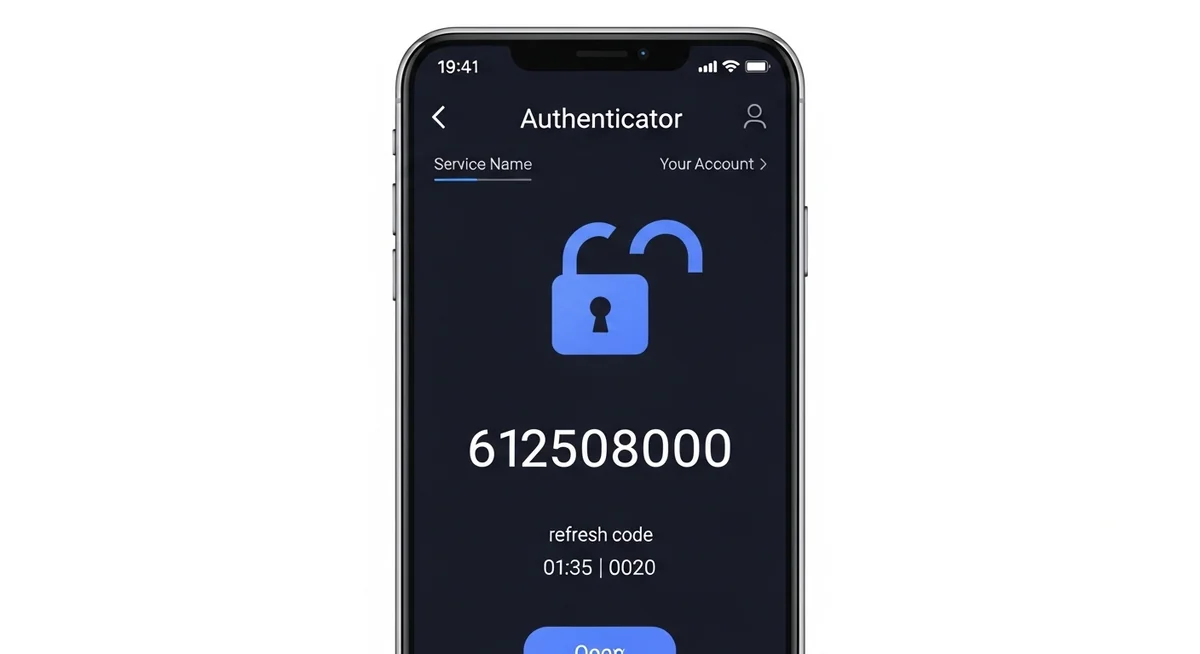
Two-Factor Authentication (2FA)
- SMS-based codes (less secure, susceptible to SIM swapping)
- Authenticator apps like Google Authenticator, Authy, or Microsoft Authenticator (more secure)
- Hardware security keys supporting FIDO2 standard (most secure)
According to cybersecurity researchers, over 80% of account compromises stem from reused passwords and social engineering rather than technical exploits.
Login Verification
- Notifications sent to registered email and phone when new devices access accounts
- Geographic location alerts for unusual login locations
- Device fingerprinting to recognize trusted devices
- Challenge questions for suspicious activity
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
Security Checkup Tools
- Active session monitoring showing all logged-in devices
- Password strength indicators
- Connected apps review showing third-party access
- Login history showing access times and locations
Never enter your credentials on third-party websites promising free account access. These sites harvest your own login data instead.
Account Protection Features
- Encrypted direct messages (rolled out gradually since 2023)
- Protected tweets limiting visibility
- Blue verification with enhanced security for subscribers
- Advanced filtering for potentially harmful content
What About Legal Consequences of Unauthorized Access?
Attempting to hack a Twitter account or any other social media profile constitutes serious criminal activity in virtually all jurisdictions:
United States
- Computer Fraud and Abuse Act (CFAA): Unauthorized access to computer systems carries penalties up to 10 years imprisonment
- State computer crime laws: Additional state-level charges often apply
- Wiretapping laws: Intercepting communications can trigger additional charges
- Identity theft laws: Using someone else’s credentials may constitute identity theft
According to cybersecurity researchers, over 80% of account compromises stem from reused passwords and social engineering rather than technical exploits.
European Union
- GDPR violations: Unauthorized data access can result in substantial fines
- Computer Misuse Act (UK): Up to 10 years imprisonment for unauthorized access with intent
- National cybercrime laws: Individual EU countries maintain additional cyber offense statutes
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
Other Jurisdictions
Most developed nations have similar laws criminalizing unauthorized computer access, with penalties typically including:
- Prison sentences ranging from months to years
- Substantial fines (thousands to hundreds of thousands of dollars)
- Restitution payments to victims
- Permanent criminal records affecting future employment
- Civil lawsuits from victims seeking damages
- Restraining orders or protective orders
Notable Prosecutions
In 2020, three individuals were arrested for the massive Twitter hack that compromised over 100 high-profile accounts including Barack Obama, Elon Musk, and Bill Gates.The attackers used social engineering to gain access to Twitter’s internal tools. Despite being teenagers, they faced federal charges and substantial prison sentences.Numerous other cases have resulted in multi-year prison sentences for attempting to hack Twitter accounts and other social media platforms, even when no financial gain was realized. Law enforcement takes these crimes seriously, particularly when they involve prominent accounts or widespread disruption.
What About Protecting Your Own Twitter Account?
Understanding how attackers try to hack Twitter accounts helps you better protect your own:
Essential Security Measures
- Enable two-factor authentication using an authenticator app (not SMS)
- Use a unique, complex password generated by a password manager
- Never reuse passwords across different services
- Regularly review active sessions and revoke unfamiliar devices
- Review and remove unnecessary connected apps
- Use a unique email address for your Twitter account if possible
- Enable login verification alerts
- Protect your associated email account with equal security measures
Never enter your credentials on third-party websites promising free account access. These sites harvest your own login data instead.
Understanding these risks helps you make better decisions about your account security and online behavior.
According to cybersecurity researchers, over 80% of account compromises stem from reused passwords and social engineering rather than technical exploits.
Behavioral Practices
- Never click suspicious links, even from apparent contacts
- Verify URLs before entering credentials (check for https:// and exact spelling)
- Don’t respond to unsolicited messages requesting account information
- Be cautious about publicly sharing personal information used in security questions
- Regularly update your recovery email and phone number
- Monitor your account for unauthorized posts or messages
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
Advanced Protection
- Consider using hardware security keys (YubiKey, Google Titan Key)
- Enable encrypted direct messages when available
- Use a VPN when accessing Twitter from public Wi-Fi
- Keep your devices’ operating systems and apps updated
- Install reputable antivirus software
- Regularly back up important data
What About Ethical Hacking and Security Research?
If you have genuine interest in cybersecurity and understanding vulnerabilities, legitimate career paths exist:
Bug Bounty Programs
Twitter/X operates a bug bounty program through HackerOne, paying security researchers for responsibly disclosing vulnerabilities. Payouts range from hundreds to tens of thousands of dollars depending on severity. This provides legal compensation for security research while improving platform security for all users.
Cybersecurity Careers
The cybersecurity industry faces a severe talent shortage, with excellent compensation and job security:
- Penetration testing: Legally testing organization security with permission
- Security analysis: Monitoring and responding to threats
- Incident response: Investigating and remediating breaches
- Security engineering: Building secure systems and applications
- Risk assessment: Evaluating organizational security posture
Never enter your credentials on third-party websites promising free account access. These sites harvest your own login data instead.
Entry-level positions often exceed $70,000 annually, with senior roles commanding $200,000+ in major tech markets.
Educational Resources
- Cybersecurity certifications (CISSP, CEH, OSCP)
- Online platforms like TryHackMe, HackTheBox, and Cybrary
- University programs in cybersecurity
- Capture The Flag (CTF) competitions
- Security conferences like DEF CON and Black Hat
What About Alternatives to Hacking?
If you’re considering hacking someone’s Twitter account, consider these legal alternatives:
For relationship concerns:
- Direct conversation about trust issues
- Couples therapy or counseling
- Deciding whether the relationship is sustainable without trust
According to cybersecurity researchers, over 80% of account compromises stem from reused passwords and social engineering rather than technical exploits.
For parental oversight:
- Open conversations about social media safety
- Following your child’s public account
- Age-appropriate monitoring with transparency
- Education about online risks rather than surveillance
Always keep your device updated and use strong unique passwords with two-factor authentication to minimize security risks.
For business concerns:
- Competitive intelligence through public information
- Social media monitoring tools for brand protection
- Legal discovery processes if litigation is involved
“Digital security is a shared responsibility. Parents monitoring their children, employers securing company devices, and individuals protecting their own accounts all contribute to a safer ecosystem.”
Dr. Sarah Chen, Digital Forensics Expert, SANS Institute
What About Conclusion?
Hacking Twitter accounts is neither easy nor legal. The platform employs sophisticated security measures making unauthorized access extremely difficult for anyone without advanced technical skills. Even if you succeed, the legal consequences are severe, potentially including years in prison and substantial fines.More importantly, attempting to hack a Twitter account violates fundamental ethical principles of privacy and respect. Whether targeting a stranger, celebrity, or intimate partner, such actions demonstrate a willingness to violate others’ rights and trust.If you have concerns justifying your interest in someone’s Twitter account, legal and ethical alternatives almost always exist. Direct communication, therapy, legal counsel, or simply accepting you can’t control others’ behavior all represent more constructive approaches than violating laws and ethics.For those genuinely interested in cybersecurity, numerous legitimate career paths offer excellent compensation and the satisfaction of protecting rather than violating others’ security. The choice between becoming part of the solution versus part of the problem ultimately defines your character and determines your future.Protect your own accounts, respect others’ privacy, and choose legal and ethical paths forward. The temporary information gained from hacking rarely justifies the lasting consequences that inevitably follow.
Frequently Asked Questions
Can someone really hack my account without me clicking anything?Zero-click exploits exist but are extremely rare and expensive — typically reserved for state-level surveillance of journalists and politicians. The vast majority of hacks require user interaction: clicking a phishing link, downloading malware, or entering credentials on a fake site.
What should I do immediately if I think my account was hacked?Change your password from a different device immediately. Enable two-factor authentication if not already active. Check active sessions and revoke any you don't recognize. Review recent account activity for unauthorized changes. Contact the platform's support team to report the compromise.
Are those 'hack any account' websites and tools real?No. Every website or tool claiming to hack accounts for free or a small fee is a scam. They either steal your payment information, install malware on your device, or harvest your own credentials. Legitimate security researchers never offer hacking services to the public.
How can I tell if my password was leaked in a data breach?Check haveibeenpwned.com — enter your email to see which breaches include your data. For each match, change that password immediately. Use a password manager to generate unique passwords for every account so one breach doesn't compromise everything.
What is the single most effective step to protect my accounts?Enable app-based two-factor authentication (Google Authenticator or Authy) on your email account. Your email is the master key — compromise that, and attackers can reset passwords for virtually every other account you own. App-based 2FA blocks over 99% of automated attacks.